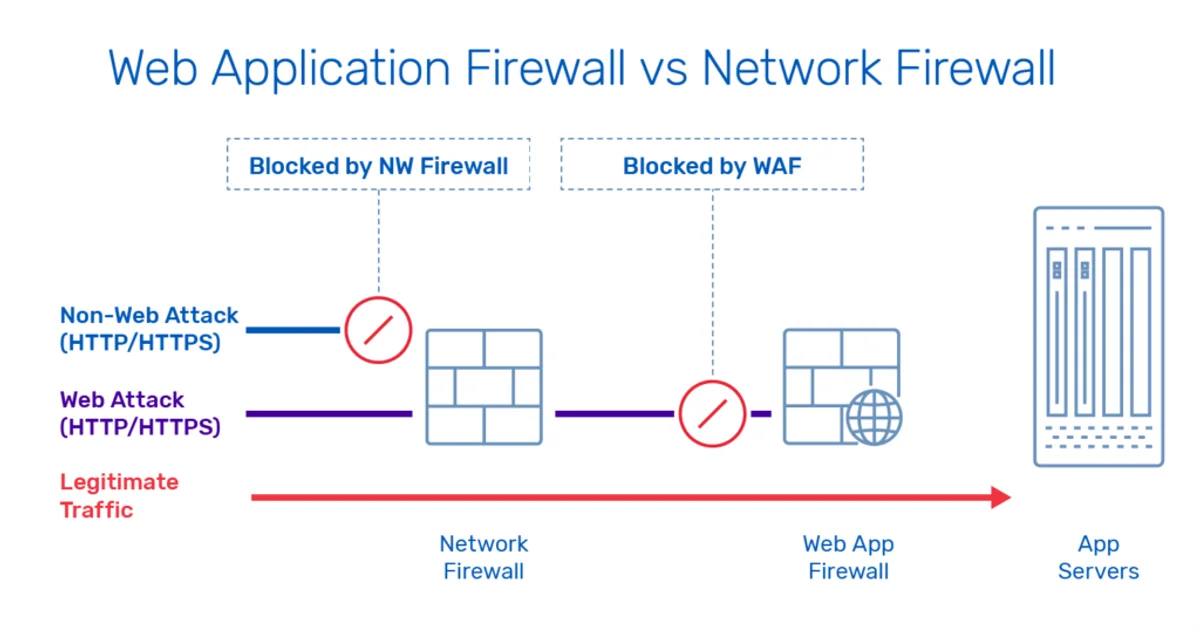
Network Firewalls vs WAFs: Understanding Your Defense Layers
Network firewalls filter by IP and port at Layer 3/4. WAFs inspect HTTP content at Layer 7. Learn when you need each and how to configure them together.
Secure your infrastructure and applications. TLS certificates, OAuth 2.0 flows, firewall rules, zero trust architecture, and vulnerability management for production systems.
8 articles
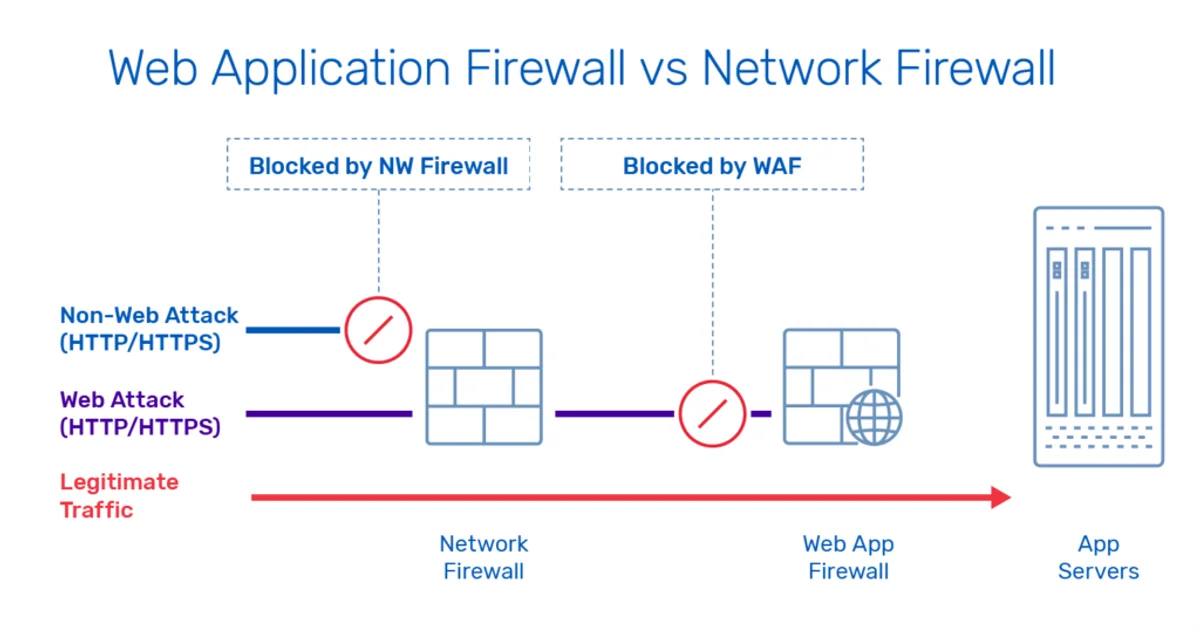
Network firewalls filter by IP and port at Layer 3/4. WAFs inspect HTTP content at Layer 7. Learn when you need each and how to configure them together.
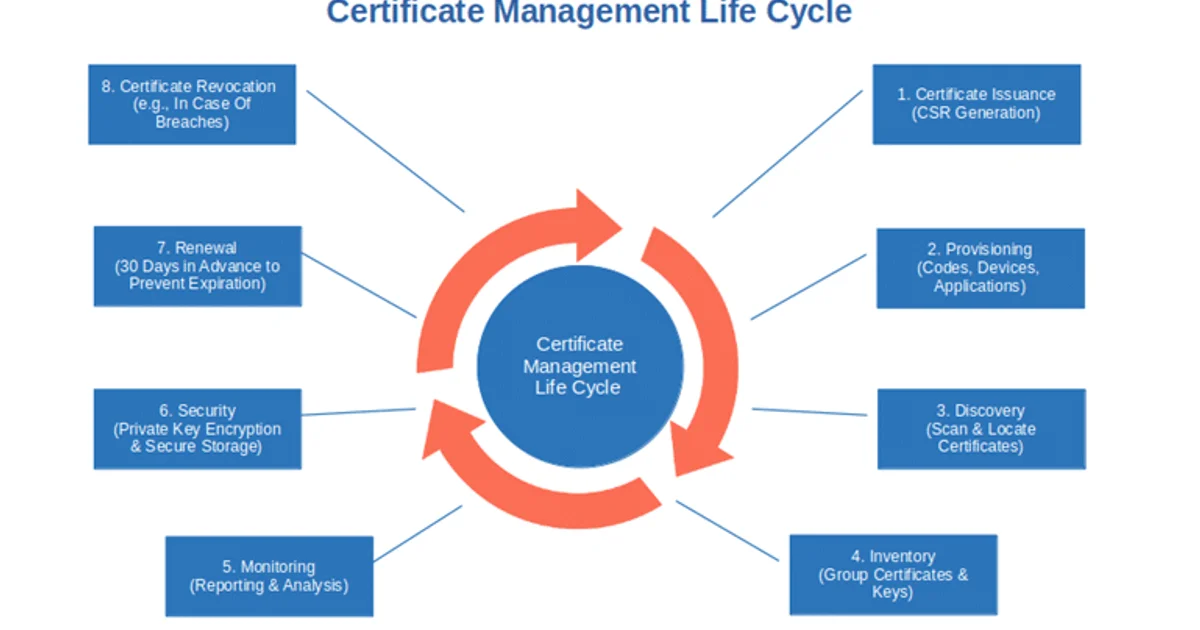
Automate TLS certificates with Let's Encrypt, ACME protocol, and cert-manager in Kubernetes. Covers HTTP-01, DNS-01, wildcards, private CAs, and expiry monitoring.

SSRF lets attackers reach internal services through your server. Learn how cloud metadata endpoints amplify the risk and how to defend against SSRF.
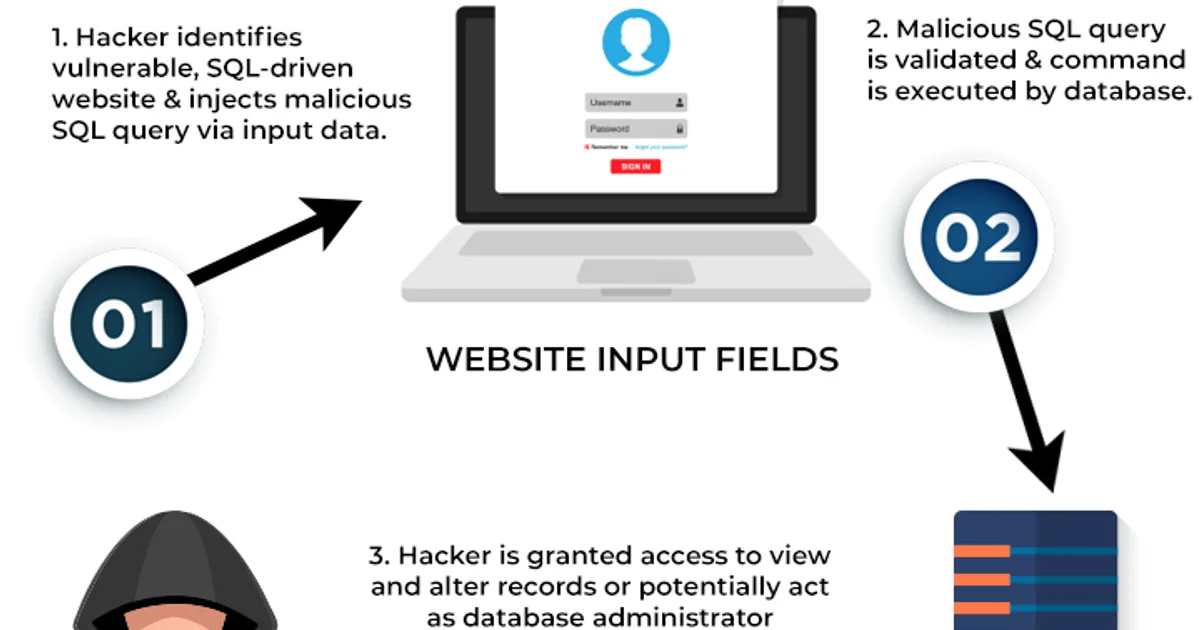
SQL injection remains a top vulnerability. Learn how SQLi works, why ORMs are not enough, and how to prevent it with parameterized queries and defense in depth.

Compare Vault, AWS Secrets Manager, and Kubernetes Secrets. Learn about dynamic secrets, rotation, injection patterns, and when to use each tool.
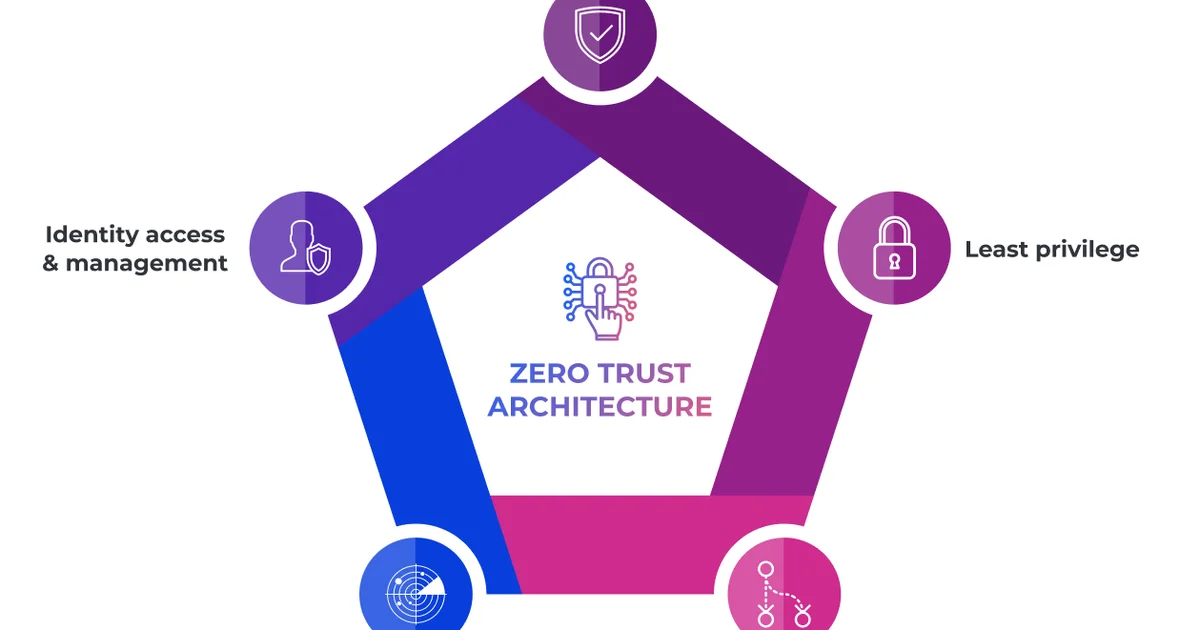
Zero Trust eliminates implicit trust based on network location. Learn the five pillars, mTLS, SPIFFE/SPIRE, and a practical implementation roadmap.
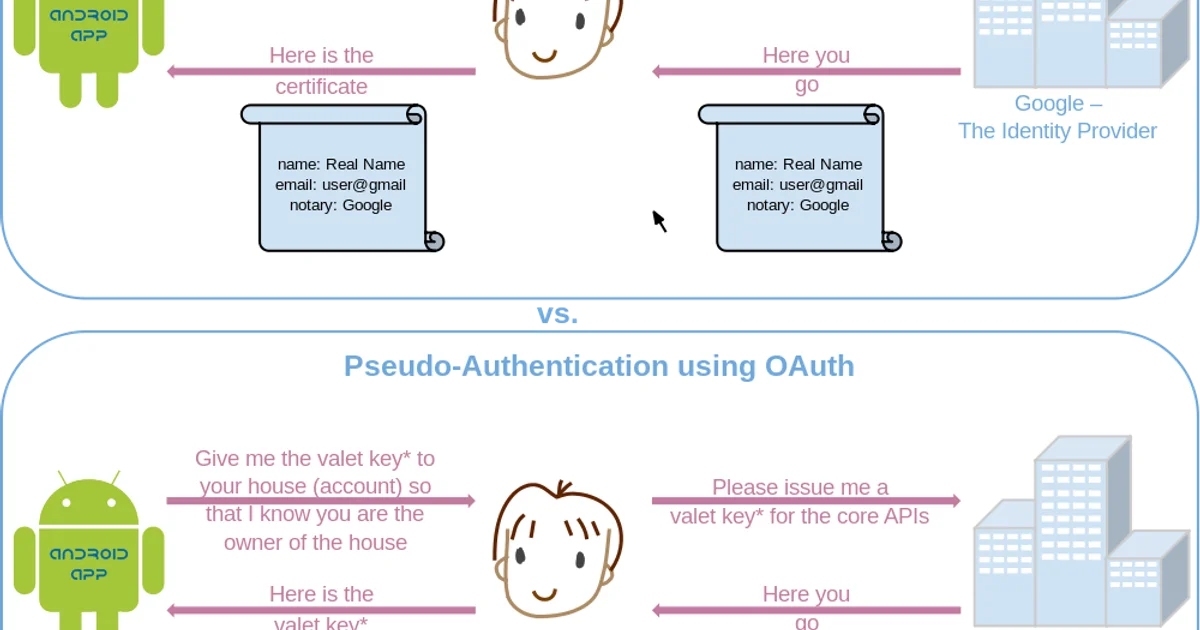
OAuth 2.0 handles authorization while OIDC handles authentication. Learn the grant types, token differences, PKCE, and when to use each protocol.
An honest comparison of JWT and session token authentication. Covers JWT structure, signing algorithms (RS256 vs HS256), common vulnerabilities, the revocation problem, and when each approach is the right choice for your architecture.
New articles delivered to your inbox. No spam.